Today, phones are not just an amalgamation of chips, metal pieces, and other electronic components whose primary job was to establish wireless communication. It has now transformed into an emerging species which gets evolved with time to come out as the fittest among the other manufacturing companies which compete to serve mankind in the technological front. The one who loses is ticked off the list. Hence the law of “survival of the fittest” is pretty much applied to these new-age species called SMARTPHONES too. The emergence of this form of a smartphone, which has a mind of its like a human, can be termed as “Artificial Intelligence”. In this article, we are going to talk about how to Boost the Security of your Device.
Related – How to Fix Google Play Services has Stopped Working.
Understanding the Security
Android can be comprehended to be the soul of the smartphone. Without Android, your smartphones could be lifeless just like humans without their breath. The reason you can make the most of your applications on your smartphone is Android. Let us imagine for your phone to be a luxurious bungalow, and Android(Operating-system) is the key to your bungalow. without you can never get into your fancy bungalow and have the best out of it. Here your key is something which connects you to your house of dreams.
Now, in this bungalow, imagine having all your mobile applications, right from WhatsApp to Instagram. The scariest part is, Bigger the bungalow bigger the chances of robbery.
And in this bungalow, the most precious thing prone to be filched is our “DATA.” Nothing more than a home full of applications, which is an abundant source of personal data could make a burglar elated. And for a better word of familiarity, these burglars are called hackers or cyber attackers or cyber criminals. They are out there on their toes to prey on your data and use it for their greedy intentions. Hence, your bungalow, i.e., your Android device, requires the highest notch of security to safeguard your data. Similar to Android, macOS, or iOS is the bungalows or the devices manufactured by Apple.
Android Security Practice to Boost the Security of Your Device:
Android renders a multi-tasking, multi-touch, android beam, Wi-Fi Direct, Web browser, and excellent connectivity. Because of these characteristics, your bungalow or your Android device recumbent towards the exploitation of your data. Just like, if your house has too many entrances, the easier it gets for the burglar to barge in.
1. Android Security Patch Level
To tackle security issues, it is very imperative to estimate the issues that may arise, analyze the issues that had occurred in the past, and concede the issues that are inherently embedded at the time of manufacture. Android security patch level ought to update. With the literal meaning of “patch,” it is a dynamic change to the software by applying a specific code.
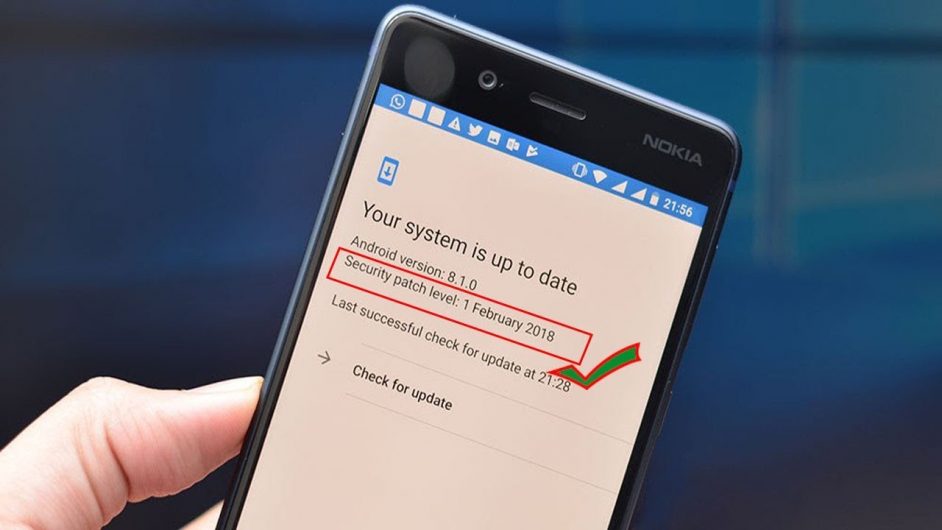
The security patch is a subset of AOSP (android open source project) and includes a bulletin, which displays different types of vulnerabilities in the Android device and the fixes to them.
The security patches address the security issues described in the bulletin. The bulletin will gets updated on a monthly basis. Manufacturing companies also display their product’s vulnerability details exclusively.
This updation and the awareness of the security patches would make you aware of the threats to the security system. Hence, we suggest frequent checking of the bulletin to the customers.
2. Knox
Samsung Knox is an inbuilt security software with an exceptional set of security features in Samsung Android devices. Knox is very user-friendly, and its automated updation characteristics strengthen the security of the device.

Devices without the Android OS, i.e., Mac devices, can also use Knox by installing it from the official website. This minimizes the chances of showing the hidden files on Mac. In Samsung devices, the security software is free but requires constant updation to fix the issues.
Read – Best Free Unlimited VPN Applications for Android.
3. Maintenance of a Secure Folder
This is the most suggestive measure and a user-friendly one too. Storing all the confidential and personal data in a folder or a file and securing it with a smart lock, therefore, it will seclude the data from any anonymous approach.
When it comes to the Mac, it has the edge over Android in this case as it’s easy to hide the files for security concerns. This could be done with the help of a feature called “Finder” on Mac.
Finder hides the folders from the view and also doesn’t display the folder on default. This is how we can show the hidden files on Mac. Showing and hiding of files becomes relatively easier on macOS than on Android.
In Android, hiding a folder could be a tedious task. It is also crucial to maintain a backup and restore of the data in the secure folder of the Android device. Hence, showing of hidden files on Mac becomes a boon to the macOS in terms of security.
4. Phone Encryption
Phone encryption must be a vital practice. Because when we restart the device, screening of all the data becomes necessary to prevent easy access to unknown users. Opting for face recognition or fingerprint.
The lock will increase the strength of security in case you misplace your device or undergoes any manipulation externally. A very strong password should be assigned when it comes to your macOS devices to enable Encryption and to avoid the reachability to your view or show your hidden files on Mac.
5. Google Play Protect
Google Play Protects a popular application or software, which is a package of security elements that do the work in the background and notify you at the identification of any threat to your device’s security.
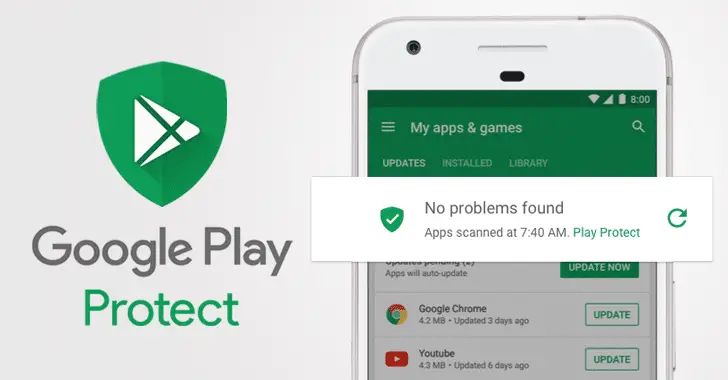
The most amusing feature about this is, it automatically scans all the applications that you install in your device and disables the malicious app until you uninstall it from your device. This application even takes care of your device’s “App permissions,” which closes the door to any malware practices.
6. Anti-malware Installation
Android is open-source, which makes it much more prone to malware attacks. Hence, the installation of anti-malware would act as a guard to your device at the time of browsing i.e., at the time of maximum exposure to malicious websites and viruses.
Anti-malware is advised to be installed in macOS devices that would eliminate all the risks of disclosure of hidden files on Mac. Suggested anti-malware would be Kaspersky, Avast, F-secure SAFE, McAfee, etc.
7. Find My Device
It is an application by Google that is now inbuilt in all Android devices as it is the service provided. This helps us with the location and remotely controlling the device when the method is not in your reach or goes missing.
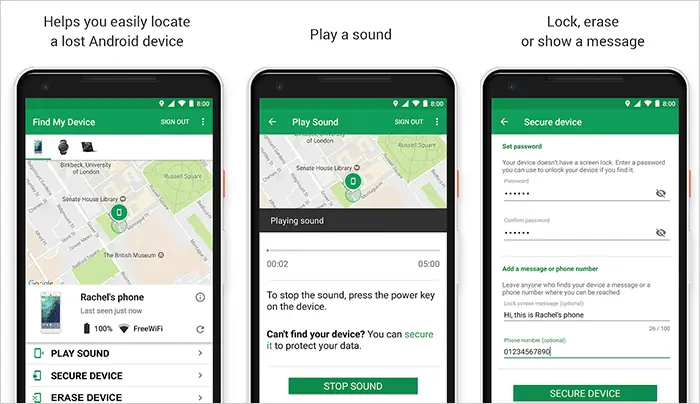
This would automatically lock you when enabled and also erase the data on your phone by having a backup of it. When you lock your phone, you can add notification reminder messages which will display on the lock screen, such as your phone number, etc.
8. Credential Storage
In credential storage, all the certificates be it user and security certificates that are given by trusted companies. We should make sure to enable all the certificates because these certificates prove whether the website is trusted or untrusted.
When a certain website doesn’t get approved by a certain certificate of a company, a notification has been generated.
More – How to Play Android Games on PC/Laptop.
9. SIM Card Lock and Encryption
Your SIM holds contacts which of inestimable worth for you as well as the cyber attacker. Hence you should protect it by all means possible. Securing your SIM with a PIN would make the data in the SIM card encrypted and would only be unencrypted only when the right PIN is entered.
10. Pinning Windows
You can pin your windows in an extreme case of security and deliberately to save the device from any further exposure. The pinning of windows is nothing like but a virtual wall that will be an app, behind which all the other applications would be hidden, and access to those apps would be denied, and the user should comply with this mode, and no PIN is helpful here in this security measure.
More – 10 Most Downloaded Apps on Play Store.
Basics
- Always have a lock on your lock screen. Make sure to keep a PIN, fingerprint or face recognition as your priority
- Always take care of the software updates and update it as soon as it is notified to you.
- Make sure to always remember to log out of your accounts if you log in from devices apart from your devices.
- Always link your data with the Google account.
- Always BACK UP AND RESTORE.